Ransomware Bitcoin Demands And How Coinfirms Investigations Help
Content
A ‘bitcoin’ unit of currency is represented as a ‘BTC’ and can be traded for real-world currency through various exchanges. The Bitcoin client software that is run on computers in the P2P network is open source, as well as the bitcoin-mining software that exists to support the system. And it’s exactly these features that have encouraged the adoption of Bitcoin by the dark forces of the online world as well, with cybercriminals and malware authors taking a keen interest in this new technology. But before we delve into the agglomeration of nefarious activities surrounding Bitcoin, we need to have a basic overview of what bitcoins are and how the Bitcoin system works. Social and technological change often creates new opportunities for positive change. So, when a new system of currency gains acceptance and widespread adoption in a computer-mediated population, it is only a matter of time before malware authors attempt to exploit it.
This computational problem is in fact a 256-bit value, which in Bitcoin terminology is called the target for a block. Note that Bitcoin users can also store their wallet data via other means, such as through websites that store their Bitcoin wallet instead of keeping their wallet data on their machine. By default, the original Bitcoin client stores this data in a file on the local system called ‘wallet.dat’.
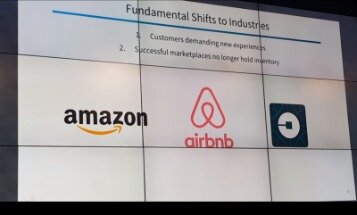
Failure to make this distinction is arguably one of the reasons why blockchain is yet to fully take off, added Halliwell. Another drawback is the staggering amount of electricity currently required to power a blockchain system — a sticky point for many businesses hoping to reduce their energy consumption as part of a wider sustainability push. Despite the new challenges which technology presents, doing things digitally can actually be safer than in-person, said Sanders.
However, you may delete and block all cookies from this site and your use of the site will be unaffected. By continuing to browse this site, you are agreeing to Virus Bulletin’s use of data as outlined in our privacy policy. Office malware has been around for a long time, but until recently Excel Formula 4.0 was not something researcher Kurt Natvig was very familiar with. In this article Kurt allows us to learn with him as he takes a deeper look at XF 4.0. For the wallet-stealing functionality, it uses a shell script to dump the contents of the wallet, which by default is located at ‘~/Library/Application Support/Bitcoin/wallet.dat’, to a file named ‘dump.txt’, as can be seen in Figure 13. Win32/Minepite.A is distributed as a Nullsoft installer that installs an executable with the fi le name bcm.exe, a popular miner developed by Ufasoft .
Where Is Bitcoin Accepted?
Customers using Android and iOS versions 5.0.2 through to 5.1.0 of its Copay app are affected, it warned. What makes this latest attack unusual is that the hackers were able to access the accounts at the system level, rather than just individual accounts, meaning it is unknown exactly what other damage could potentially be caused. As well as Jeff Bezos and Barack Obama, other high-profile accounts including rapper Kanye West, investor Warren Buffett, Microsoft co-founder Bill Gates, and the corporate accounts for Uber and Apple.
To further strengthen cross-jurisdiction collaboration we will soon be announcing an intelligence alliance. The initiative will add strength to the ecosystem of more than 200 financial institutions, cryptocurrency exchanges and protocols leveraging Coinfirm’s RegTech solutions and will aid practical financial crime work to combat a $6 trillion problem. The AMLT Network is the first-of-a-kind crypto crowdsourcing intelligence system where victims can report suspicious cryptocurrency addresses related to ransomware – alerting us to new and ongoing attacks – and be rewarded in AMLT, the native token. The other is Reclaim Crypto, a solution for victims to reclaim their cryptocurrency by launching crypto investigations, some of which are cases of ransomware.
A number of celebrity Twitter accounts have been hacked in an apparent cryptocurrency scam designed to solicit digital currency. The reason so much Bitcoin is lost is that the network is not overseen by any single entity, so there is no safety mechanism to prevent loss. Decentralization is part of what attracts many people to the world of cryptocurrency, but it also involves playing with fire to some extent.
And at times, this fund traded 200% above net asset value, which is dripping with crazy sauce. To its credit, Bitwise hasn’t shied away from the premium that the fund’s structure has created. It tweets it out to very little backlash, and in fact got more “likes” than I would expect.
Another Bitcoin Backdoor Opens
But the fact that many businesses, including online stores and retailers, are now accepting bitcoins also plays a factor in its increased usage. Some online retailers, providing products such as clothing, home accessories, electronics, books, music, consumables, the list goes on, see bitcoins as a legitimate payment method. As previously mentioned, the role of the miner nodes connected to the Bitcoin network is to solve a computationally difficult problem tied with transactions before they are accepted into the block chain.
As mentioned previously, bitcoins can be exchanged for real-world currencies, and a number of Bitcoin exchange websites exist that facilitate these exchanges. The first one established was the Bitcoin Market on 6 February 2010, and over the years more exchanges have surfaced, with the Bitcoin wiki listing about 66 exchanges. Bitcoin-mining and -stealing functionality has been discovered in a number of the most notable and prevalent malware families, including Alureon, Sirefef and Kelihos. Notably, Bitcoin being open-source software means that Windows users are not the only target. Cross-platform attacks have already been seen, with OS X threats such as MacOS_X/DevilRobber.A emerging on the scene in October 2011.
Every time a problem is solved, the network adds a new ‘block’ to a chain that is set at 1MB in size. With each solution, the miner is rewarded a number of bitcoins that remains constant. The number of Bitcoins generated per block started at 50, and has halved every 210,000 blocks, or every four years. In order to read or download cryptocurrency the 10 biggest trading mistakes newbies make and how to avoid them ebook, you need to create a FREE account. Similar to previous malware we’ve observed targeting bitcoins, DevilRobber uses the same technique of installing a freely available program to execute its bitcoin-mining payload. The trojan installs the OS X GPU version of the popular miner DiabloMiner, with file name ‘DiabloMiner-OSX.sh’, using a script named ‘miner.sh’, as well as executing a CPU miner named ‘minerd’. Bitcoin may not be as anonymous as it seems, as mentioned by a Bitcoin core development team member, Jeff Garzik, in the same Gawker article.
Over the past year two major ‘forks’ in Bitcoin, where community groups had different ideas about how to make improvements to Bitcoin’s underlying blockchain, leading to the creation of new cryptocurrencies based on Bitcoin. As it is almost impossible to predict the value of the currency in the long term, or to judge how difficult it will be to mine, there are still too many uncertainties for some. There is also concern that the network will become oversaturated and unusable, as more people flood the mining community and make Bitcoin mining too difficult. Bitcoin is also incredibly easy to use, and there is no need to go through bank applications to set up an account.
Prominent Celebrity Twitter Accounts Hacked In Apparent Bitcoin Scam
Additionally, the number of bitcoins created through this mining process is in fact controlled by the system. The difficulty of the target that is set for each block being worked on is adjusted collectively by the network every 2,016 blocks so that, on average, six blocks are solved per hour. This difficulty can increase or decrease, depending on how quickly the last 2,016 blocks were generated by the miners. If the network finds that miner nodes generated the blocks too quickly, the difficulty is increased, ‘to compensate for increasing hardware speed and varying interest in running nodes over time’, as Nakamoto explained in his paper. In order to read or download cryptocurrency the 10 biggest trading mistakes newbies make and how to avoid them pdf ebook, you need to create a FREE account. Once present on a network, Prometei will deploy a number of modules to perform anti-analysis and security checks before connecting to a command and control server over HTTP, Tor, or I2P.
This is probably a means by which the Sirefef authors attempt to thwart AV products that rely on emulation to detect these malware families and the bitcoin miner. Sirefef is a sophisticated, multi-component malware family that uses stealth techniques to hide itself on a compromised computer and communicate with other remote peers using a P2P protocol. Sirefef has multiple parts to it, and is capable of performing a number of payloads, including modifying Internet search results, generating pay-per-click advertisements, downloading additional malware, replacing system drivers, as well as bitcoin mining. Bot herders would undoubtedly find the Bitcoin system’s distributed computing technique a tempting prospect.
The worm is programmed to launch Internet Explorer in the background and direct the browser to the Bitcoin Plus generator page, ensuring the compromised user is unaware they are generating bitcoins for the account holder through the Bitcoin Plus Java applet. First described in a Gawker article on 1 June 2011, Silk Road is an online drug marketplace that allows visitors to browse through a library of illegal drugs and purchase them from sellers located around the world using bitcoins exclusively. Access to Silk Road is only possible through Tor , a system that enables online anonymity by encrypting and routing Internet traffic through a network of relays run by volunteers. This combination of accessing the site through the Tor network and buying with bitcoins makes it difficult for authorities to track these purchases.
First Macosx Bitcoin Backdoor
The accounts have had to have some of their activities limited, including preventing some verified accounts from publishing messages for several hours. It said it would restore access only when it was certain it could do so securely. Twitter says that hackers used employee access through the backdoor of their systems to take control of the accounts. According to one of the world’s leading cryptographers, Bitcoin’s elliptic curve could have a secret backdoor, invalidating all underlying security. You would think these turbulent splits would’ve proved disastrous for Bitcoin, yet all signs suggest they did little to impede its momentum. Prices barely moved after the creation of Bitcoin Cash, and Bitcoin Gold has had even less impact so far.
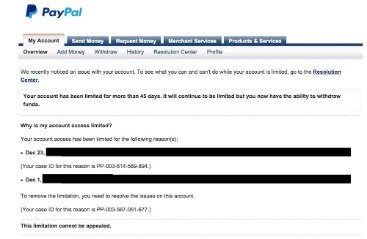
It’s maintained by a peer-to-peer network, free of centralised management, and is almost impossible to edit. Bitcoins are stored in a digital wallet that is saved to a user’s PC or in the cloud. The wallet acts like a virtual bank account, allowing users to pay for goods and services by sending Bitcoins to another wallet. Despite the recent downturn in the cryptocurrency market, Bitcoin remains the most well-funded and most traded digital currency in the world. Zhou said that he first noticed that something was wrong when he received several emails regarding a password reset for their Rackspace account. Afterwards he connected to the Bitcoin wallet server via SSH and “found that everything gone.” The crypto has a vibrant futures market trading on CME, and it’s being requested by investors everywhere.
In comments made by Zhou on online forum bitcointalk.org, the thieves struck at a server hosted by Rackspace. Issuers see the demand for a vehicle that offers easy access to crypto currencies, even at a steep price.
You can expect more of these types of alternative structures surrounding bitcoin to begin multiplying at a rapid rate as money flows into these products in the states, or in Germany or in Sweden. And importantly, the regulatory exemption under which this exists has been applied and has existed for many years and predates crypto, to be sure. The reason for that is bitcoin has a regulated futures market on the CME and other assets don’t. People who buy the shares using the ticker BITW in their Fidelity account or whatever can buy and sell them intraday in the same you can an ETF. This is a model that was pioneered by Grayscale, which is another crypto asset manager, with a fund called GBTC, which many people are probably familiar with. I could rattle off the terms and exemptions under which it exists from a regulatory perspective, from the SEC and FINRA, etc., but they wouldn’t mean much to you.
To provide incentive to those willing to volunteer their computers for this task, the network awards bitcoins to the account of the miner that generated the correct hash to validate a block. This is why they are referred to as ‘miners’, since this is the way in which bitcoins come into existence. Due to the increase in miner nodes and thus the increase in difficulty of solving blocks, many find that, depending on their processing power, it can take anything from days to years to solve a block while solo mining. This is why pooled mining is popular, since a pool’s combined processing power means blocks are hashed and solved at a faster rate, and participants receive a steady stream of bitcoins for their contribution. There are many mining pool servers online, and as we shall see later, use of these mining pools is common among malware writers.
We saw a report by Symantec showing that in ideal conditions, a botnet of 100,000 infected machines could earn its botmaster $97,000 USD a month. That was in June 2011, and we’ve seen how volatile the value of a bitcoin has been since then. The flocks of Bitcoin users choosing to mine for bitcoins means that solving blocks will continue to get more difficult because that’s simply how the system is designed. So if we recalculate (using the Bitcoin Mining Calculator online tool) the monthly earnings, this time using today’s difficulty ( .847444) and bitcoin exchange rate ($5.246 USD), we find earnings of $10,000 USD. We also discussed illegal trade involving bitcoins, with the online drug market Silk Road being used for the sale and purchase of illicit drugs using bitcoins as its sole payment method due to its apparent anonymity. But we also saw that Bitcoin isn’t as anonymous as it seems, with research published showing that using different network inspection techniques, it is possible to identify Bitcoin users.
- Just select your click then download button, and complete an offer to start downloading the ebook.
- This is probably a means by which the Sirefef authors attempt to thwart AV products that rely on emulation to detect these malware families and the bitcoin miner.
- Additionally, the number of bitcoins created through this mining process is in fact controlled by the system.
- If crypto owners choose to keep their holdings in a non-custodial wallet, outside of an exchange, forgetting or losing the private key becomes a fatal mistake.
Nakamoto set it up this way to control the total currency generated in the network, so that by 2040 no more than 21 million bitcoins in total will be in circulation. At the time of writing, 183,249 blocks have been solved, meaning approximately 9.1 million BTCs are in circulation.
Additionally, plenty of hackers are offering ransomware as a service , essentially letting anyone hire a hacker from DNMs. Both purchasing/leasing ransomware and hiring black hat hackers are services that can be paid for in cryptocurrency. However, not every organization is foresighted enough to deploy blockchain data risk management solutions and much work happens after the fact, i.e. after a ransom note is received. Hospitals are soft targets for attackers; organizations with valuable data , heavily bureaucratic (unable to function without their well-oiled system), often reliant on legacy technology and pressed for time . REvil, Sodinokibi, Nemty, Nephilim, NetWalker, DoppelPaymer, Ryuk, Maze, CLOP, Tycoon and Sekhmet – brand names to a malicious few, fear inciting to everybody else – were some of the top ransomware viruses last year. According to Kroll – Coinfirm’s strategic partner in forensic crypto-crime investigations – the threat was the most observed year-to-date of cyber incident response cases, accounting for over one-third of all.